AsiaTechDaily – Asia's Leading Tech and Startup Media Platform

Enterprises Are Deploying AI Faster Than They Can Govern: Why Identity Is Becoming Critical
Okta’s latest blueprint highlights how enterprises can better manage AI agents as they scale across APAC. As adoption accelerates, identity can emerge as a key foundation for visibility, control, and accountability.
On April 30, 2026, Okta made its Okta for AI Agents platform generally available, bringing to market a new framework designed to help enterprises manage the growing complexity of AI-driven systems. At the core of this launch is Okta’s “secure agentic enterprise” blueprint, which introduces a structured approach to governing AI agents by answering three fundamental questions: where these agents exist, what they can access, and what actions they are allowed to perform
The blueprint is built around a key shift—treating AI agents as identities that must be discovered, registered, governed, and, if necessary, instantly deactivated. It includes capabilities to detect both sanctioned and “shadow” agents, assign ownership, control access across applications and APIs, and enforce real-time policy decisions, including the ability to revoke access through a centralized “kill switch” when agents behave unexpectedly
That challenge is particularly evident across Asia Pacific. According to Okta’s Businesses at Work 2026 report, enterprises in the region are accelerating AI adoption across workflows, customer interactions, and core operations. However, this growth is not being matched by identity readiness. As AI agents, bots, and service accounts proliferate—often outnumbering human users—only a small proportion of organizations report having the systems in place to securely manage them.
While several identity and security vendors are expanding their capabilities to manage non-human identities, the idea of treating AI agents as fully accountable, identity-bearing entities—on par with human users—remains an emerging practice. In most organizations, governance frameworks have yet to evolve to this level, leaving gaps in ownership, visibility, and control as AI systems scale.
In an exclusive conversation with AsiaTechDaily, Dan Mountstephen, Senior Vice President and General Manager for APJ at Okta, discussed how this imbalance is reshaping enterprise security, highlighting the rapid rise of non-human identities, the growing prevalence of “shadow AI,” and the need for organizations to rethink identity as the central control layer for increasingly autonomous systems.
These developments point to a widening gap between AI adoption and governance. As enterprises move toward more autonomous, agent-driven environments, identity is emerging not simply as a security function, but as the central control plane required to manage access, enforce policy, and maintain trust at scale.
Adoption Outpaces Governance
The pace of AI adoption across APAC is no longer incremental. Enterprises are embedding AI agents into workflows, customer interactions, and internal systems, fundamentally reshaping how work is executed. According to a recent report, more than 90% of organizations are already using AI agents in some capacity, though most remain in early or limited stages of deployment.
Whilst, the scale of non-human identities is expanding rapidly. In many environments, these identities can outnumber human users by significant margins, introducing a new layer of operational complexity. Despite this, only a small fraction of organizations feel fully equipped to manage and secure them—highlighting a widening gap between technological capability and governance maturity.

This imbalance is further compounded by the way AI adoption is unfolding within enterprises. Rather than being centrally orchestrated by IT teams, the current wave of AI deployment is often driven by employees experimenting with tools and integrating them into daily workflows.
As Mountstephen explains:
“There is a significant gap between those who have effective security, governance, and policy controls and the mass adoption happening in every function—marketing, sales, manufacturing, or legal. The big difference from previous technology waves, like the cloud, is that this AI wave is largely being driven by us as people and users rather than IT organizations. That is leading to enormous amounts of ‘Shadow IT.’
Every person I speak to gives consistent feedback: LLMs are springing up everywhere, and CISOs and IT organizations are playing catch-up. They are trying to figure out how to let the organization use these tools while fulfilling their duty of care to shareholders and ensuring they don’t end up as headline news for a breach.”
This decentralized adoption model is accelerating innovation—but also creating significant blind spots in visibility, accountability, and control.
The Rise of Non-Human Identities
We are seeing a rapid expansion of non-human identities. Unlike traditional service accounts, modern AI agents are increasingly autonomous, capable of executing workflows, accessing systems, and even spawning additional agents to perform specialized tasks.
This fundamentally changes how identity must be managed.
“Agents tend to have a huge amount of permissions that are far-reaching. If you don’t have the right infrastructure and an agent spins up its own sub-agent, there is no plan of record for what they are doing. They can potentially go off and access very sensitive data, which is why this is so topical,” Mountstephen noted.
Traditional identity systems were built around predictable human behavior—employees with defined roles, access levels, and lifecycle stages. AI agents, by contrast, are dynamic, scalable, and non-deterministic. They operate at machine speed, often without direct human oversight, and interact with multiple systems simultaneously.
The result is what many organizations are now experiencing as identity sprawl—a rapid increase in the number and complexity of identities that must be managed across the enterprise.
Identity as the Primary Attack Surface
As identity ecosystems expand, so too does the associated risk. The fundamental mechanics of cybersecurity have not changed: most breaches still begin with compromised credentials, followed by lateral movement and privilege escalation.
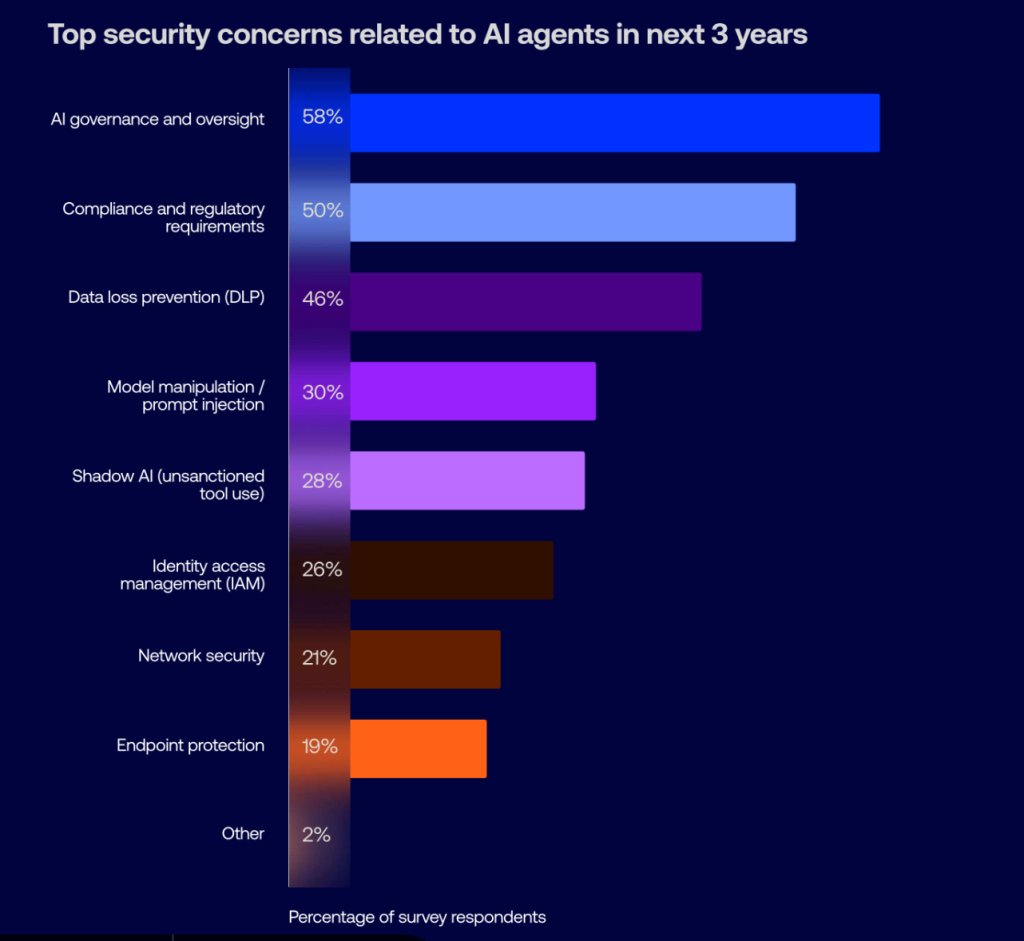
However, AI is amplifying both the speed and scale at which these risks can materialize. According to recent report, identity-based attacks continue to dominate the threat landscape, with credential misuse remaining a primary entry point for breaches. As autonomous agents gain access to sensitive systems and data, a single compromised identity can trigger cascading effects across an organization’s digital environment.
Mountstephen emphasized that the core challenge lies in visibility:
“You can’t protect what you can’t see. For me, it all starts with continuous audit visibility and understanding your posture. We have Identity Security Posture Management, which is continually scanning the environment for things like orphaned accounts.
A common situation is someone spinning up cloud instances for a project, moving on, and forgetting to take them down. Or a marketing team setting up their own LLMs or note-taking tools without telling IT. Step one is identifying where everything is, including sanctioned agents and Shadow IT, to understand the ‘blast radius.’”
As these unmanaged systems accumulate, organizations struggle to maintain a clear view of what exists within their environment, what access has been granted, and how different systems are connected. This makes it harder to assess risk, contain potential threats, or respond effectively when something goes wrong.
From Identity Management to Identity Infrastructure
This shift is forcing a redefinition of identity itself. As enterprises move toward agentic AI, identity is evolving into a continuous, dynamic system that governs access, behavior, and trust across both human and non-human actors.
Okta’s blueprint for the secure agentic enterprise is a framework introducing a broader model of identity governance. It treats AI agents as “first-class identities” within the enterprise.
This includes:
- Discovering and registering both known and “shadow” agents
- Enforcing access controls across applications, APIs, and data systems
- Enabling real-time revocation of access through mechanisms such as universal logout
At a conceptual level, the model shifts identity from a static directory to a control plane—a central layer that determines how systems interact, what actions are permitted, and how risk is managed in real time.
This shift is also reflected in broader industry research. According to a recent report from Gartner, identity and access management is being reshaped by the rise of AI agents, requiring new approaches to identity registration, governance, and policy-driven authorization for machine actors.
The report notes that traditional identity models, designed primarily for human users, are increasingly inadequate as autonomous agents become active participants in enterprise systems—expanding the need for continuous visibility, control, and accountability.
APAC: A High-Growth, High-Risk Environment
The Asia Pacific region presents a particularly complex landscape for this transition. Rapid digitization, combined with diverse regulatory environments and hybrid IT infrastructures, is accelerating both AI adoption and associated risks.
According to Okta’s report, APAC is seeing strong growth in hybrid and on-premise environments, further complicating identity governance. As organizations connect legacy systems with cloud-based AI platforms, maintaining consistent identity controls becomes increasingly challenging.
At the same time, the region’s pace of innovation means that governance frameworks are often still evolving.
“We are seeing this play out very clearly across APAC, where organizations are moving quickly to adopt AI, but are still building the governance models needed to support it. This isn’t just about managing more users; it’s about managing entirely new classes of identity that don’t behave like humans and operate at a completely different scale,” Mountstephen said.
As enterprises move deeper into the agentic AI era, the competitive landscape is shifting. The ability to deploy AI quickly is no longer the primary differentiator. Instead, organizations are increasingly judged by their ability to deploy it responsibly.
Mountstephen frames this transition clearly:
“If you automate anything at scale, the risk scales with it. The organizations that will lead in this next phase won’t be the ones that move fastest, but the ones that can demonstrate control, accountability and governance as they deploy AI.
That’s why identity is becoming the control plane for the modern enterprise—it’s what enables organizations to manage access, enforce policy and maintain trust as environments become more complex.”
The emergence of agentic AI marks a turning point in enterprise technology. As autonomous systems become embedded in business operations, the question is no longer whether organizations can adopt AI—but whether they can govern it.
For enterprises across APAC, the challenge ahead is clear. Scaling AI will require more than infrastructure investment or model deployment—it will demand a rethinking of identity as the foundation of control, accountability, and trust in the modern enterprise.
The Next Phase of Identity: From Access Control to Autonomous Governance
What is emerging in this space is not a single product shift, but a structural reset of how enterprise security is designed. Across the industry, identity is moving from a control point for human access to a foundational layer governing autonomous systems. AI agents are introducing behaviors that traditional systems were never built to handle, including continuous authentication, dynamic privilege escalation, and autonomous decision-making across interconnected systems.
In response, the identity market itself is being reshaped. Vendors are converging around the idea of unified identity platforms that can manage human, machine, and AI identities together, shifting away from fragmented tools toward continuous, policy-driven architectures. However, this transition remains incomplete. Most enterprises still operate with legacy IAM models, fragmented visibility, and manual governance processes that are fundamentally misaligned with machine-speed environments.
As a result, the defining challenge ahead is not technological capability but operational discipline. Organizations will need to rethink identity as infrastructure—embedding visibility, ownership, and real-time control into every layer of their systems. Those that succeed will be able to scale AI with confidence, while those that do not risk creating environments where automation expands faster than accountability.
| About Okta: Okta is an identity and access management company that provides secure access solutions for enterprises, developers, and organizations worldwide. Its platform enables authentication, authorization, and lifecycle management for users, applications, and devices across cloud and hybrid environments. |
Quick Takeaways
- AI agents are scaling rapidly across APAC enterprises, becoming embedded in workflows, customer interactions, and core operations.
- Non-human identities are expanding faster than governance frameworks, creating new challenges in visibility, control, and accountability.
- Okta’s “secure agentic enterprise” blueprint introduces a structured approach to managing AI agents through identity, focusing on discovery, access control, and real-time enforcement.
- Treating AI agents as identity-bearing entities marks a shift toward accountability, where every agent must have ownership, permissions, and lifecycle management.
- The identity layer is evolving into a central control plane, enabling organizations to govern access, enforce policies, and manage risk in autonomous environments.
- Enterprises that align AI adoption with strong identity governance will be better positioned to scale securely and maintain trust.